Blockchain 0x000 – Understanding the Fundamentals
When it comes to my FYP project at university I wanted to touch something new. I did not want to choose AI, LLMs etc. Web3 and Blockchain technologies appeared to be great topic for me.
It's a blooming area, a lot to research so why not choose. I discussed with my other two team members and decided to go with a BlockChain related project. That's how I got into this awesome area. And then I started to go deep in to Blockchains, Web3 technologies etc.
Imagine a world where strangers can exchange money, share data, or execute agreements without ever needing to trust a central authority. No banks, no intermediaries, no single point of failure yet everything remains secure, transparent, and verifiable.
That’s the promise of blockchain technology a distributed, tamper-resistant ledger that has transformed how we think about trust in the digital world.
While most people first hear of blockchain through Bitcoin or cryptocurrencies, its principles go far beyond finance. From supply chains to digital identity, healthcare, and voting systems, blockchain’s decentralized design has inspired innovation across industries.
In this article, we’ll explore blockchain from the ground up how it works, what problems it solves, and why it’s considered one of the most significant technological shifts since the advent of the Internet.
By the end, you’ll understand not only what blockchain is, but why it matters and how its core ideas are shaping the future of trust, transparency, and security.
Meet the characters.
If hou ever read our cryptography related articles, these guys are not new to you. Alice, Bob, Trudy, and Eve are friends with a vision.
They want to create a banking system where they can send money to each other and keep track of transactions.
They are going to build a financial system. Let’s say a bank. The primary goal is to do transactions between them and keep track of these.
At first, they think it’s simple: “We just need a ledger!” But soon, they realize that trusting a single person or authority to manage the ledger is risky. Mistakes, fraud, or cheating could happen.
This is where blockchain technology comes in. Through their journey of building a “trustless” bank, we’ll explore the core ideas behind blockchain distributed ledgers, hashing, consensus mechanisms, smart contracts, and security.
Chapter 1: The Problem Trust in a Central Bank
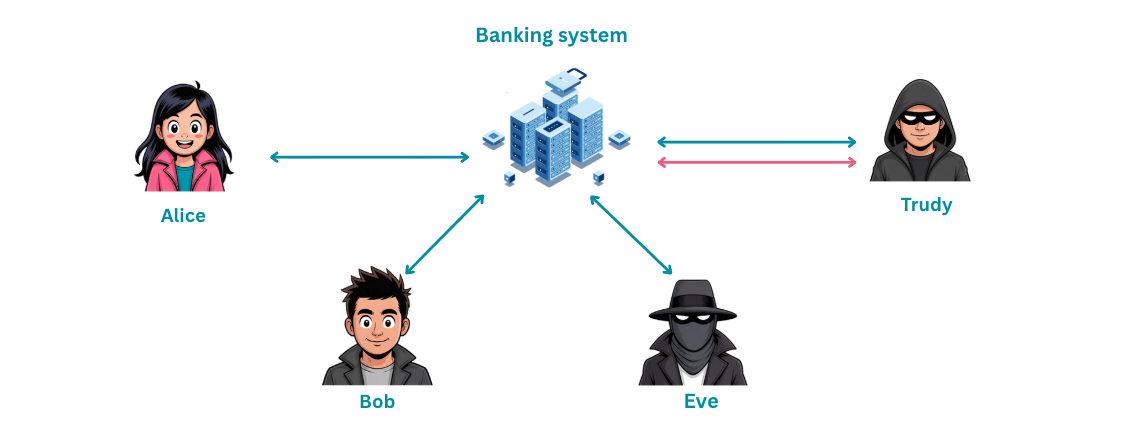
Alice wants to send $10 to Bob. Simple enough, right?
Option 1: They ask a central authority say, a bank to record the transaction.
But here’s the thing. Centralized systems come with centralized risks:
- What if the bank makes a mistake or worse, tries to cheat?
- What if Trudy tries to spend the same $10 twice? This is known as the double-spending problem.
- What if Eve tampers with the records when nobody’s looking?
They realize that trusting a single person or institution is risky, especially in the digital world where copying data is trivially easy. A digital dollar isn’t like a physical coin you can duplicate it with a copy-paste.
Blockchain solves this by removing the need for trust in a central authority replacing it with mathematical proofs, consensus, and cryptography.
Chapter 2: Creating a Ledger
The friends decide to start simple. They write down every transaction in a shared notebook:
| Sender | Receiver | Amount | Timestamp |
|---|---|---|---|
| Alice | Bob | $10 | 10:00 AM |
| Bob | Trudy | $5 | 10:05 AM |
At first, it works. But soon, they notice problems:
- Someone could erase or alter a transaction.
- It’s hard to verify the accuracy of the ledger if multiple people want to check it.
- Who controls the notebook? Whoever holds the pen holds the power.
This is where the idea of immutability comes in transactions need to be tamper-proof. Once something is written, it should be permanent. No erasers allowed.
Chapter 3: Linking Transactions The Birth of Blocks
Alice suggests a clever idea:
“What if each page in the ledger includes a summary of the previous page?”
She’s essentially describing a hash chain and it’s a brilliant concept.
Think of a hash as a digital fingerprint. You feed in some data, and a hash function spits out a unique, fixed-length string. Change even a single character in the data, and the entire fingerprint changes. It’s like sealing each page in the notebook with a wax stamp that contains an imprint of the previous page’s contents.
Here’s what that looks like in practice:
Block 0 (Genesis Block)
├── Transactions: [Alice → Bob: $10]
├── Timestamp: 10:00 AM
├── Previous Hash: 0000000000
└── Hash: a4f2e8c1d9...
Block 1
├── Transactions: [Bob → Trudy: $5]
├── Timestamp: 10:05 AM
├── Previous Hash: a4f2e8c1d9...
└── Hash: 7b3d91f0e2...Each block contains a hash of the previous block. If someone tampers with a transaction in Block 0, its hash changes and now Block 1’s “Previous Hash” field no longer matches. The chain breaks. Everyone will know immediately.
The ledger has become a chain of blocks a blockchain.
This solves the problem of tampering. The chain links all past transactions securely, and any attempt to rewrite history sticks out like a sore thumb.
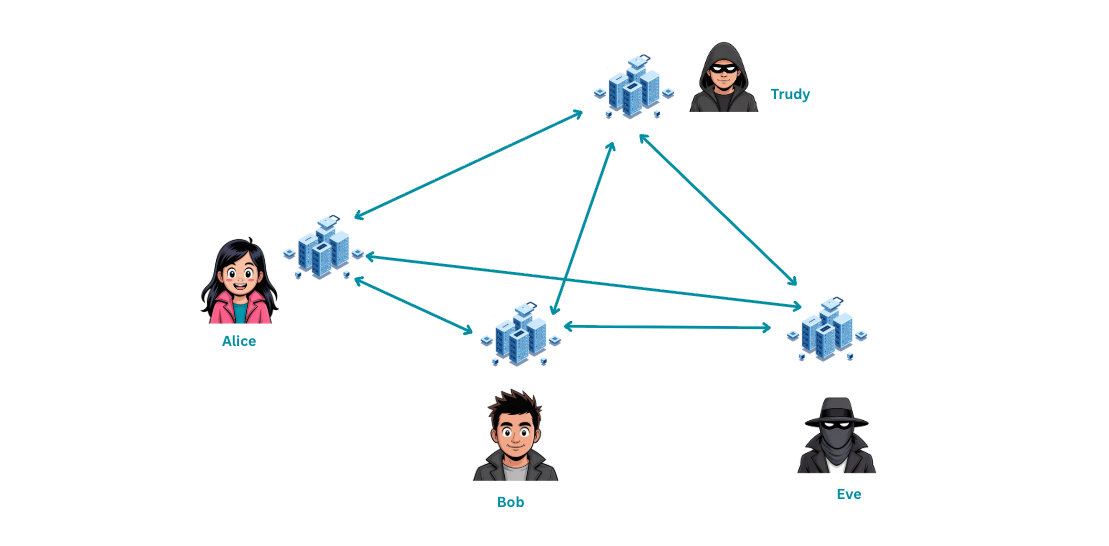
Chapter 4: Decentralization Everyone Keeps a Copy
But there’s still a weakness. If only one person holds the notebook, they could quietly tamper with all the blocks and recalculate the hashes. Problem solved for the attacker.
So the friends decide on something radical instead of one notebook, each friend keeps a full copy of the ledger.
- Alice has a copy.
- Bob has a copy.
- Trudy has a copy.
- Eve has a copy.
Now if Trudy tries to cheat and alter her copy, the other three copies will immediately expose the inconsistency. The majority rules.
This is the essence of a distributed ledger multiple participants verify and store the same information, removing a single point of failure. There’s no central server to hack, no single database to corrupt. You’d have to compromise the majority of the network simultaneously and in a large blockchain network with thousands of nodes, that’s practically impossible.
Chapter 5: Mining & Consensus Who Writes the Next Page?
The friends now face a new problem: if everyone has a copy of the ledger, who gets to write the next page?
If anyone can add a block at any time, chaos ensues. Conflicting blocks, duplicate transactions, and disagreements everywhere.
Bob suggests a game:
“What if we make it hard to add a new block? You have to solve a difficult mathematical puzzle first. The winner gets to add the next block and everyone else checks that it’s valid.”
This is Proof of Work (PoW) the first widely used blockchain consensus mechanism, and the one that powers Bitcoin.
Here’s how it works in simple terms:
- The network presents a puzzle find a number (called a nonce) that, when combined with the block data and hashed, produces a result starting with a certain number of zeros.
- Miners compete to find this nonce. It requires massive computational effort essentially brute-force guessing.
- The first miner to find it broadcasts the new block.
- Other nodes verify the solution (verification is easy, even though finding it was hard).
- The block is added to the chain, and the winner receives a reward.
It’s like a lottery where the tickets are generated by raw computing power.
Later, the friends learn about an alternative Proof of Stake (PoS):
- Instead of solving puzzles, participants “stake” their own coins as collateral.
- Validators are selected based on how much they’ve staked the more skin in the game, the more likely you are to be chosen.
- If you try to cheat, you lose your stake. Simple but effective.
PoS uses far less energy than PoW, which is why Ethereum transitioned from PoW to PoS in 2022 an event known as “The Merge.”
The key takeaway? Consensus ensures that everyone agrees on the state of the ledger, even if some participants are dishonest. As long as the majority plays fair, the system holds.
Chapter 6: Smart Contracts Automating the Rules
The friends’ bank is working, but there’s a lot of manual overhead. Every time a transaction happens, someone has to verify the conditions, check balances, and update the ledger. What if these rules could execute themselves?
Alice proposes a new idea:
“What if we write programs that live on the blockchain and they execute automatically when certain conditions are met?”
She’s describing smart contracts self-executing programs stored on the blockchain that enforce rules without human intervention.
Think of a smart contract like a vending machine. You put in your money, select your item, and the machine dispenses it automatically. No cashier needed. No trust required. The rules are baked into the machine itself.
Here are some examples:
- “If Alice sends $10 to Bob, automatically update both balances.”
- “If Bob receives $5 from Trudy, notify Eve.”
- “If the balance in Alice’s account falls below $20, automatically block outgoing transactions.”
In the real world, smart contracts power everything from decentralized lending protocols to NFT marketplaces. Ethereum was the first blockchain to support them, and it opened the door to an entire ecosystem of decentralized applications (dApps).
The beauty of smart contracts? Once deployed, nobody can alter them not even the person who wrote them. The code is law.
Chapter 7: Security & Attacks
Now let’s talk about what happens when someone tries to break the system. Because they will try.
Trudy true to her name (think “intruder”) decides to cheat.
Attack 1: Double Spending
Trudy tries to spend the same $10 twice once to Alice and once to Bob.
But the network catches it. Every node has a copy of the ledger, and when Trudy’s conflicting transactions arrive, the consensus mechanism kicks in. Only one transaction gets confirmed. The other is rejected.
Attack 2: Tampering with Old Blocks
Trudy tries to go back and rewrite history changing a transaction from three blocks ago.
But remember the hash chain? Altering one block means recalculating the hash of that block and every block after it. In a PoW system, that means re-mining every subsequent block faster than the rest of the network combined. This is called a 51% attack, and in any large blockchain, it’s computationally infeasible.
Attack 3: Impersonation
Trudy tries to send money in Alice’s name.
This is where digital signatures come in. Every participant has a pair of cryptographic keys:
- A private key kept secret, used to sign transactions.
- A public key shared openly, used to verify signatures.
Only Alice’s private key can authorize transactions from Alice’s account. Without it, Trudy can’t forge a signature. It’s like having a magical lock that only your unique key can open and anyone can verify the lock is authentic.
Through these mechanisms hash chains, consensus, and public-key cryptography blockchain secures transactions against fraud and malicious actors.
Chapter 8: Beyond the Bank
Alice, Bob, Trudy, and Eve look at what they’ve built and realize their system can do much more than just track money.
The same principles of decentralization, immutability, and trustless verification can be applied to almost any domain:
- Supply chain tracking: Follow goods from factory to store. Every handoff is recorded on-chain no more counterfeit products slipping through.
- Voting systems: Verify votes without a central authority. Each vote is a transaction, transparent yet anonymous.
- Healthcare records: Patients control their own medical data. Hospitals can verify records without a centralized database.
- Digital identity: Reduce fraud with self-sovereign identity you own your credentials, not a corporation.
- NFTs & DeFi: Non-fungible tokens prove digital ownership, while decentralized finance automates lending, borrowing, and trading without banks.
Blockchain is no longer just about money. It’s about building trustless systems for any digital interaction removing middlemen wherever they add friction without value.
Chapter 9: Challenges It’s Not Perfect
Even with all these innovations, the friends notice their blockchain has some serious challenges:
Scalability: Bitcoin processes about 7 transactions per second. Visa handles around 65,000. That’s a massive gap. When the network gets busy, transactions slow down and fees spike.
Energy consumption: PoW mining consumes enormous amounts of electricity. At its peak, Bitcoin mining used more energy than some small countries. PoS helps, but it’s not a silver bullet.
Privacy: On a public blockchain, everyone can see every transaction. That’s great for transparency but terrible for privacy. Do you really want the world to see your entire financial history?
Regulation & interoperability: Different blockchains operate in isolation Bitcoin can’t natively talk to Ethereum. And governments are still figuring out how to regulate this technology without stifling innovation.
But the community isn’t standing still. Solutions are being actively developed:
- Layer 2 networks (like Bitcoin’s Lightning Network or Ethereum’s rollups) process transactions off-chain and settle them on-chain dramatically increasing throughput.
- Zero-knowledge proofs allow you to prove something is true without revealing the underlying data a breakthrough for privacy.
- Cross-chain protocols and bridges are working to connect different blockchains into one interoperable ecosystem.
Wrapping Up
We started with four friends who just wanted to send money to each other. What they built through trial, error, and clever thinking mirrors the evolution of blockchain technology itself.
From a simple shared ledger to a decentralized, cryptographically secured, self-executing financial system every layer was added to solve a real problem. Trust, tampering, consensus, automation, security each chapter addressed a fundamental challenge.
Blockchain isn’t magic. It’s math, cryptography, and game theory working together to create systems where trust isn’t required because verification is built in.
Whether you’re a developer looking to build on Web3, a security enthusiast curious about the cryptographic foundations, or just someone trying to understand what all the hype is about the fundamentals we covered here are the foundation everything else is built on.
In the next article, we’ll go deeper. We’ll look at how hashing actually works under the hood, explore real blockchain data structures, and start writing code. Until then welcome to the rabbit hole.